Port Forwarding Using AWS System Manager Session Manager

Session Manager is a fully managed AWS System Manager (SSM) capability that allows you to monitor infrastructure instances, edge devices, virtual machines (VMs), and on-premises servers.
Session Manager provides a secure and auditable way to manage your infrastructure while complying with corporate policies and strict security practices across platforms.
The Problem:
Let’s say you are trying to use a GUI tool on your local machine (e.g., Sqlectron) to manage MySQL database instances inside the private subnet of an AWS VPC.
The scenario here is that we need to open a 3306 TCP port to allow connection to this database over the internet; however, this might not be the best way from a security perspective. There are several ways to connect the database securely, following AWS best practices, one of which has been explained below.
The Fix:
Follow the steps to connect the database more securely:
- Please set up a Bastion (jump host) and install all its tools. [Not recommended because that would require a lot of extra work to set up and maintain.]
- Using port forwarding in AWS Systems Manager (SSM) Session Manager can be used to connect to remote databases from a local client.
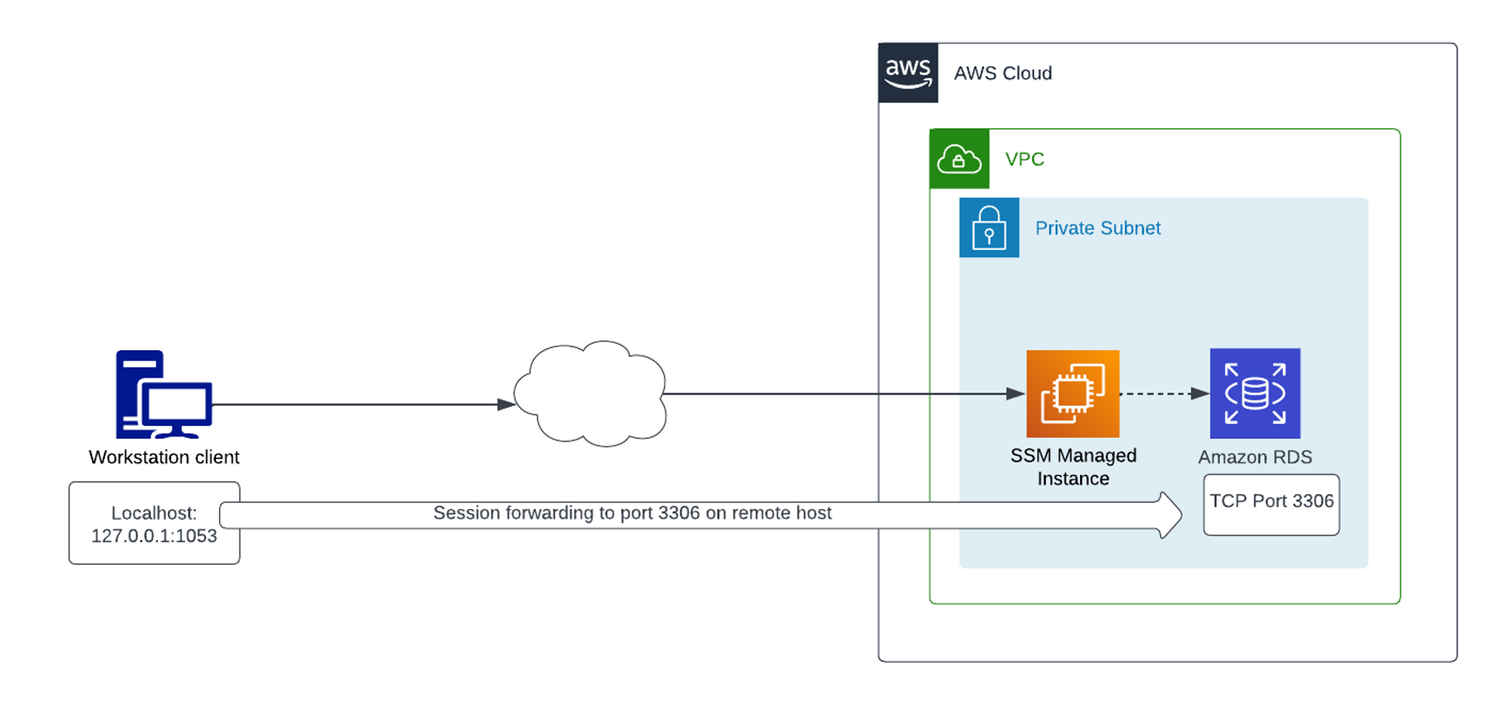
In this blog, we'll demonstrate how to use the AWS System Manager Session Manager Capability to communicate with a remote database from the local client without the hassle of setting up a jump host.
Prerequisite:
- AWS CLI is installed, set up, and configured on your local machine
- AWS credential chain is properly configured (e.g., profiles, environment variables, or IAM roles)
- AWS Session Manager Plugin is installed on your machine
- An Amazon EC2 instance is managed by AWS Systems Manager (SSM)
- The EC2 instance is in the same network as the database or has connectivity to it
- The database instance allows remote connections (no blocking rules in security groups or firewalls)
- Sqlectron is installed on your machine
Step 1: Set up SSM Managed Instance
- Create an Amazon EC2 instance
- Create an IAM role with the policy AmazonSSMManagedInstanceCore
- Assign the IAM role to the EC2 instance
- Install the SSM Agent on the instance
- Open your terminal application
- Run the following command using AWS CLI:
aws ssm start-session --target <ssm-managed-instance-id>
Replace <ssm-managed-instance-id> with your EC2 instance ID.
Note:
- Allow outbound traffic from the instance
- Ensure HTTPS (port 443) access to AWS Systems Manager endpoints
- If not using a VPC endpoint, make sure the instance has internet access
Step 2: Open a connection forwarding session to a remote port on the MySQL server
- Create an Amazon RDS instance or set up your database server on a private subnet
- Open your terminal application
- Run the following command using AWS CLI:
aws ssm start-session \
--target <ssm-managed-instance-id> \
--document-name AWS-StartPortForwardingSessionToRemoteHost \
--parameters '{"portNumber":["3306"],"localPortNumber":["1053"],"host":["remote-database-host-name"]}'
Replace <ssm-managed-instance-id> with your EC2 instance ID
Replace remote-database-host-name with your database endpoint
Note:
- Local port 1053 must be free on your machine
- You can choose a different local port if needed
- Port 3306 is the default port for MySQL
- This command creates a port forwarding session through AWS Systems Manager
Step 3: Verify Connection Forwarding Is Working (Optional)
To verify that the connection forwarding is working, run the following command in a new terminal window, which will allow you to connect to the database over the CLI session:
mysql -h 127.0.0.1 --port 1053 -u admin -p
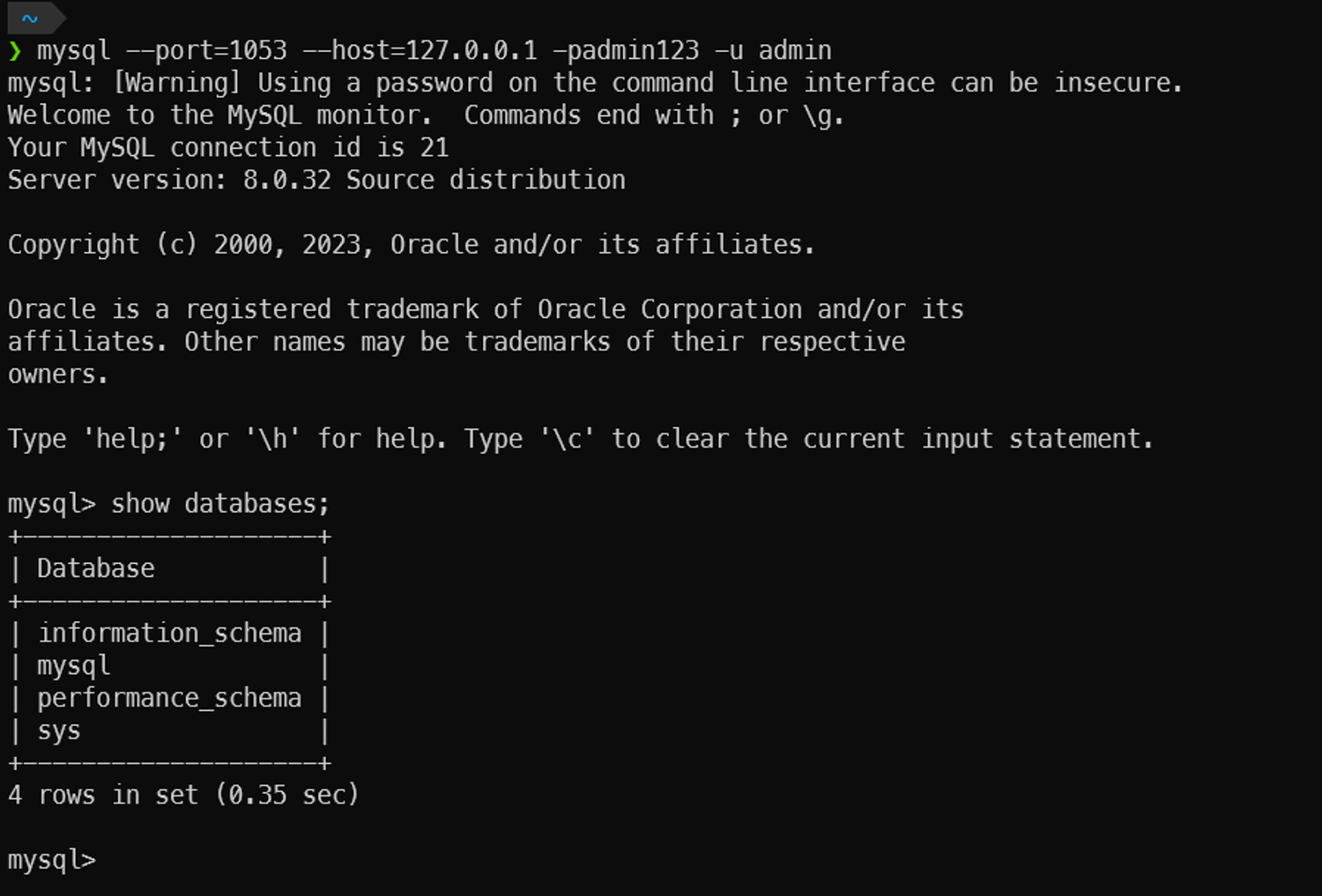
The database is connected successfully from the local using the 1053 local port.
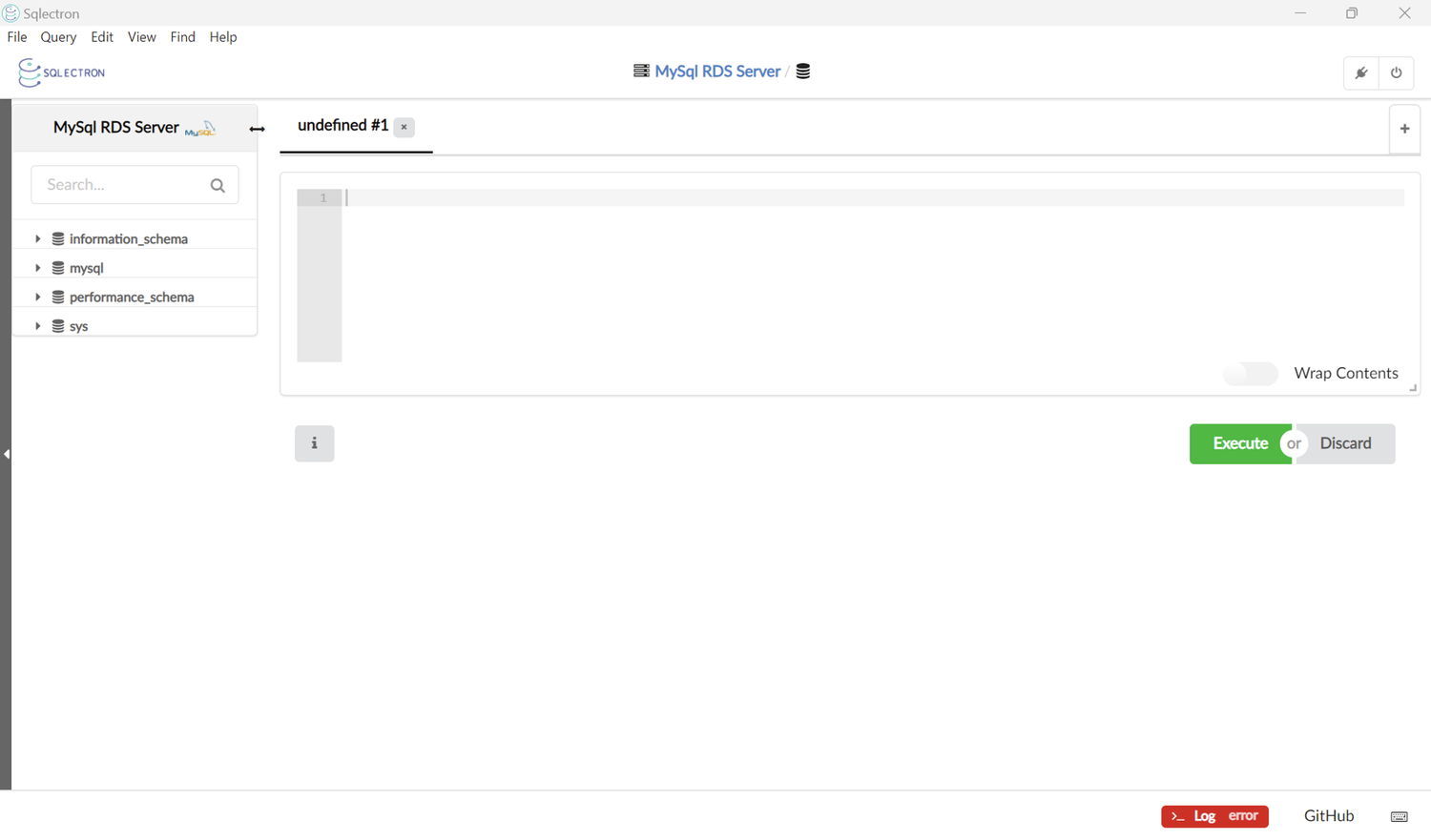
Step 4: Connect using Sqlectron
Launch SQL Sqlectron on your local machine. If you have a connection profile for this database, you may use it; otherwise, create a new profile based on the connection parameters, such as Username, Database type, and Server address, which are specific to your database.
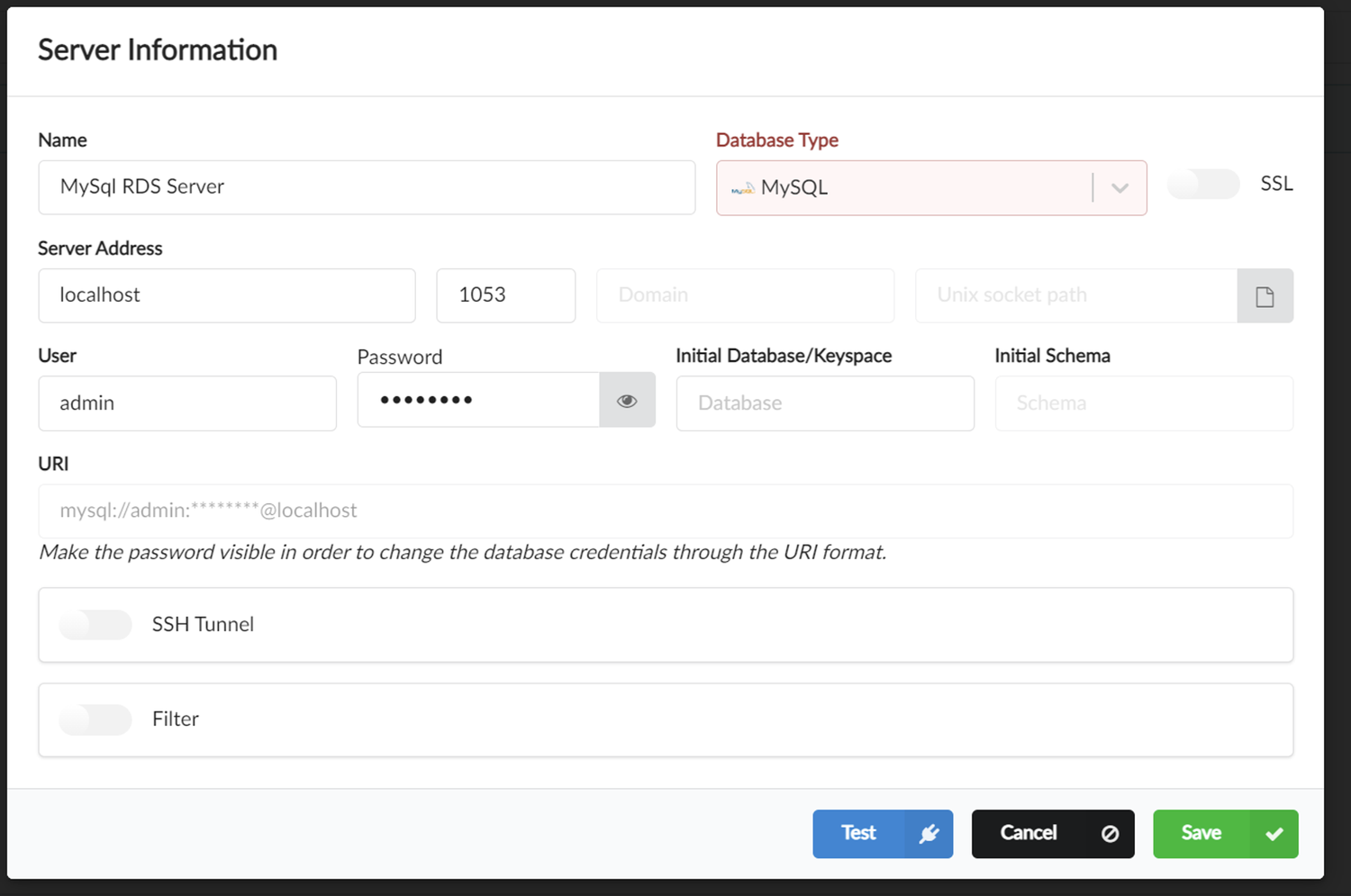
Click save, and you will be connected to your remote database.
Note: Please note that instead of using your database’s remote IP or hostname, you will use a localhost IP address or localhost in the Server field.
Conclusion:
Using AWS System Manager Session Manager to connect to a remote database from a local client is secure and effective for managing your infrastructure. In this blog, we have walked through the steps to set up a port forwarding session in order to connect your database using a GUI tool like Sqlectron.
About Author
Chandra
Author
Tech enthusiast and writer sharing insights on software development, cloud technologies, and the future of digital innovation.